-
Emergency Response Summary: Alibaba Cloud Hong Kong Computer Room Failure And Lessons Learned For Enterprise Operation And Maintenance
summary of emergency response: extract the lessons that enterprise operations and maintenance should learn from the entire history of the alibaba cloud hong kong computer room failure, covering monitoring alarms, communication processes, disaster recovery design and drill improvement suggestions to improve availability and recovery capabilities. -
Hong Kong Computer Room Bandwidth Unit’s Bandwidth Planning Suggestions For Live Video And Game Services
introduce the meaning of hong kong computer room bandwidth unit, and provide bandwidth planning, calculation and elastic expansion suggestions for video live broadcast and game services, taking into account concurrency, peak and delay control. -
Deployment Guide Teaches You To Optimize Cdn And Security In Tencent Lightweight Cloud Hong Kong Native Ip Environment
this deployment guide focuses on the native ip environment of tencent lightweight cloud hong kong. it systematically explains how to optimize cdn and security, including practical suggestions such as network planning, origin site deployment, caching strategy, https and ddos protection, monitoring and drills. -
Legal Advisors Suggest Key Items That Companies Should Pay Attention To When Signing Hong Kong Station Cluster Leasing Regulations
legal advisors suggest that companies should pay attention to key items such as contract subject matter, data protection, intellectual property rights, service levels, breach of contract and dispute resolution when signing hong kong station cluster leasing regulations to reduce legal and operational risks. -
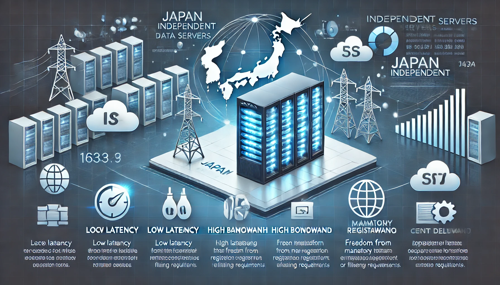
The Role And Advantages Of Hong Kong Universe Global Server In The Global Node Layout
analyze the role and advantages of hong kong universe global server in the global node layout, covering hong kong's location advantages, network connectivity, technology implementation, corporate value and compliance risks, and provide reference suggestions for decision-makers and operation and maintenance personnel. -
Select Alibaba Cloud Hong Kong Server Hosting Instance Type Strategy Based On Containerized Applications
for containerized applications, how to choose the appropriate instance type in the alibaba cloud hong kong server hosting environment: from resource characteristics, network and availability zones, storage and i/o, elastic expansion to operation and maintenance and security, practical strategies and suggestions are provided to help improve performance and cost-effectiveness. -
What Is The Role Of Hong Kong’s Native Ip Ladder In Streaming Media Acceleration And Stability?
explain what hong kong's native ip ladder is, analyze its role in streaming media acceleration and stability, including performance principles, impact of delay and packet loss, compliance and purchase suggestions, suitable for users who want to optimize their viewing experience. -
Seo Engineers Summarize How To Use Hong Kong Site Groups And The Best Solution For Adjusting The Internal Link Structure
this article is summarized by an seo engineer and introduces the usage scenarios, compliance considerations, domain name and server selection, and internal link structure adjustment of the hong kong site group, which is suitable for geo localization optimization. -
From The Perspective Of Technical Implementation, Network Architecture Suggestions For Hong Kong Site Group Multi-ip Servers To Be Exempted From Registration
discuss the network architecture recommendations for hong kong site clusters and multi-ip servers from the perspective of technical implementation, focusing on compliance, performance and security. it does not provide specific methods to avoid filing, and it is recommended to deploy within the legal framework.