this article focuses on a collection of methods to effectively defend against common network attacks on us www servers, and provides executable practical suggestions for operation and maintenance and security teams. the content covers server hardening, network and application layer protection, log monitoring and emergency recovery, taking into account performance and compliance, making it easy to implement in the north american environment.
for the us www server, the first thing to do is to harden the system and services. close unnecessary ports and services, remove default accounts, enable selinux or apparmor, tighten configuration file permissions, and use baseline configuration management tools (such as ansible/cis baseline) to ensure consistency and auditability.
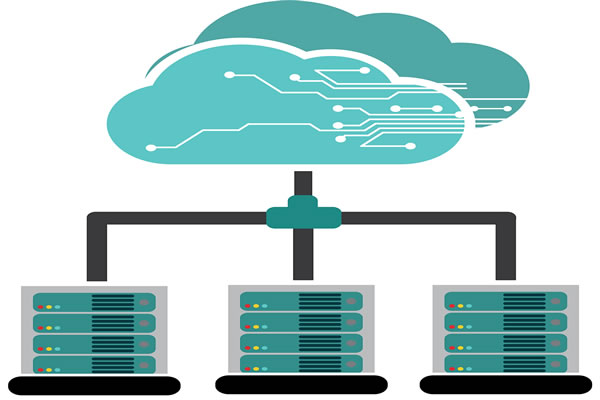
in a cloud or computer room environment, use security groups and network acls to limit traffic sources and only allow necessary ports to be opened to the outside world. deploy layered firewalls, enable rate limiting and intrusion prevention (ids/ips), and combine cdn and ddos mitigation services to reduce the impact of large traffic attacks.

the application layer is a commonly exploited attack surface, and waf should be deployed to intercept common threats such as sql injection and xss. configure regular/whitelist rules, gradually enable learning mode, and apply log adjustment strategies to ensure that false positives are controllable and have minimal impact on normal business.
strengthen remote access policies: disable password login, use public key ssh, limit login source ip, and enable multi-factor authentication (mfa). configure users and service accounts according to the principle of least privilege, and regularly review permissions and sessions to prevent lateral movement and permission abuse.
establish automated patching and release processes to promptly patch os, web servers, databases, and third-party libraries. reduce the software stack to only essential components, and use containers or immutable images to reduce the risk of configuration drift and unknown dependencies.
centralize log collection (syslog/elk/splunk, etc.), set key event alarms and retain audit logs during the compliance period. combined with siem rules, behavior analysis and anomaly detection, real-time threat discovery is achieved to ensure that security events can be quickly located and traced.
develop a verifiable backup strategy and regularly rehearse recovery procedures. backup data should be encrypted and stored separately. write and practice an emergency response plan (ir playbook), clarify contact persons, recovery steps and external communication processes to shorten recovery time.
for ddos, traffic cleaning, rate limiting and elastic expansion and contraction are used; for sql injection and xss, parameterized query, input and output encoding and content security policy (csp) are used. regularly conduct vulnerability scanning and penetration testing to verify the protection effect.
when deploying www servers in the united states, you need to consider regional regulations and data sovereignty (such as ccpa, industry compliance requirements). choose compliance areas and log retention policies, record access sources, and clarify data processing and notification obligations in contracts.
use this "security protection practice collection of methods to effectively defend common network attacks on us www servers" as a roadmap and implement it in phases: first complete boundary and identity authentication strengthening, then promote waf and log centralization, and finally establish a drill and continuous improvement mechanism. ensure long-term reliability and compliance through automation and regular audits.
- Latest articles
- How Global Websites Use Cambodian Cn2 To Improve Loading Speed For Southeast Asian Users
- Select Alibaba Cloud Hong Kong Server Hosting Instance Type Strategy Based On Containerized Applications
- Security Protection Practice: A Collection Of Methods To Effectively Defend Against Common Network Attacks On Us Www Servers
- Detailed Explanation Of Hong Kong Vps Elastic Cloud Billing Model And Cost Control Best Practices
- Comparing Various Asus Models To See The Adaptability Of Singapore's Asus Servers For Cloud Deployment
- Enterprise-level Procurement Reference Japanese Server Network Type Security And Redundancy Solutions
- Operation And Maintenance Experience Japanese Node Game Vps Pvp Server High Concurrency Optimization Plan
- Player Perspective Korean Mobile Virtual Server Supports Online Game Performance Analysis
- Singapore Dual Isp Vps Multi-line Disaster Recovery Practical And Bandwidth Optimization Guide
- What Is The Role Of Hong Kong’s Native Ip Ladder In Streaming Media Acceleration And Stability?
- Popular tags
-
Configuration And Optimization Solution For American High-defense CDN Server
This article discusses the configuration and optimization solutions of American high-defense CDN servers to help improve website performance and security. -
Analysis Of The Advantages And Usage Scenarios Of High-defense IP Server In The United States
This article will analyze the advantages of high-defense IP servers in the United States and their applicable usage scenarios to help enterprises choose the right network security solution. -
American Station Group Server Evaluation Reveals Performance And Cost-effectiveness
This article conducts a comprehensive evaluation of the American server group, analyzes its performance and cost-effectiveness, and helps users choose the appropriate server solution.