this article focuses on "case study of how much korean high-defense servers cost and their performance in actual ddos protection", analyzes the key factors that affect the price of korean high-defense servers, and discusses how to evaluate supplier capabilities through actual protection performance. the article does not provide fictitious prices, but aims to provide decision-makers with actionable evaluation ideas and purchasing suggestions.
the main factors that affect “how much does a high-defense server cost in south korea?”
factors that affect the price include peak bandwidth and cleaning capabilities, the geography and scale of the cleaning center, whether global or regional protection is included, line quality, hosting mode (physical or cloud), sla and technical support levels, and customized requirements such as application layer protection and encrypted traffic processing capabilities.
key metrics for evaluating actual ddos protection performance
measured protection performance should focus on availability, mean time to recovery (mttr), cleaning success rate, false positive rate, delay and packet loss under attacks, and processing stability of different attack types (such as syn, udp, and http floods). these indicators can better reflect value than pure price.
analysis of the relationship between cost and protective effect
price does not necessarily represent the quality of protection. higher costs usually mean greater bandwidth and more complete operation and maintenance support, but the final protection effect depends on the rationality of the protection strategy, real-time monitoring and emergency response capabilities, and whether it can maintain stable performance in actual combat.
impact of deployment model on cost and effectiveness
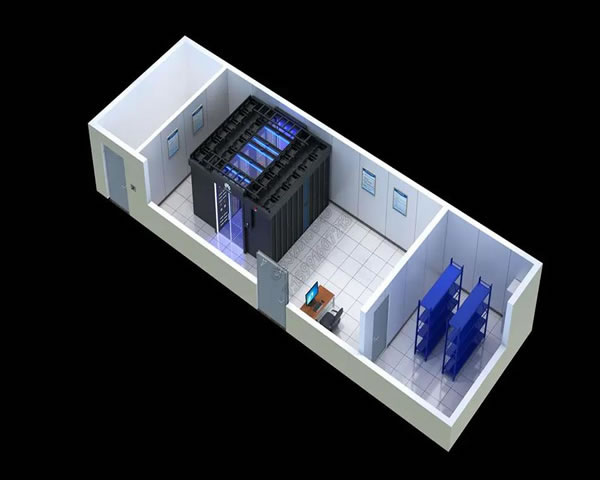
physical independent servers, virtualized instances, and cloud high-defense services each have their own advantages and disadvantages in terms of cost, elasticity, and extreme traffic carrying capacity. physical machines are more stable under extremely large traffic, while cloud services are more flexible in terms of elastic expansion and on-demand billing. the choice needs to be made based on business characteristics.
how to compare prices when you can't directly compare them
if you cannot obtain a clear price, you can evaluate the cost-effectiveness by comparing bandwidth peaks, cleaning mechanisms, historical attack disposal reports, sla details and third-party evaluations. at the same time, pay attention to whether there are hidden fees such as abnormal traffic overbilling and additional cleaning fees.
key points of real cases (excluding price information)
the case analysis should record the scale and type of attack, the supplier's cleaning methods, response and recovery time, business interruption duration, impact of misjudgment, and subsequent optimization measures. based on these points, the effectiveness of different suppliers in similar situations can be compared horizontally.
testing and validation recommendations
before purchasing, it is recommended to require a controlled stress test or view an independent test report to verify the cleaning capability and misjudgment rate; at the same time, confirm log retention, real-time monitoring, alarm mechanisms and emergency contact procedures to ensure that theoretical capabilities can be implemented in actual combat.
procurement contract and sla considerations
when signing a contract, sla indicators (availability, response time), traffic billing rules, demarcation of responsibilities, data protection clauses, failure compensation clauses and service withdrawal mechanism should be clearly defined to reduce subsequent disputes and risks arising from verbal promises.
the impact of geography and compliance on choice
when deploying in south korea or protecting korean users, you should pay attention to local network interconnection quality, legal compliance requirements, and data sovereignty issues. compliance may impact solution architecture and log retention strategies, which in turn affects overall cost and implementation complexity.
summary and suggestions
decisions about "how much does a high-defense server cost in south korea" should be driven by demand: clarify attack models and business peaks, conduct evaluations around bandwidth, cleaning capabilities, and operation and maintenance guarantees, verify the supplier's capabilities using cases and independent tests, and refine sla and billing rules in the contract to reduce procurement risks.
- Latest articles
- Community Culture Interpretation Of The Origin And Member Characteristics Of The Hong Kong Station Wolf Pack
- Steps To Deploy Vietnam Cn2 Vps From Scratch And Analysis Of Common Problems
- Summary Of Operational Suggestions For Risk Control In Malaysia Tk. Can Vps From Other Countries Be Used?
- Cn2 Singapore Vps Analysis On Seo Friendliness And Tips For Improving Site Inclusion
- Comparison And Applicable Scenario Analysis Of Taiwan’s Native Ip Phone Cards And Virtual Sim Solutions
- Interpret Common Terms And Conditions In Industry Standards And Us Server Hosting Charging Standards
- Supplier Evaluation Guide: Comparative Analysis Of Hong Kong Computer Room Blower Brands And After-sales Services
- Japanese Network Server Recommended Configuration: A Practical List For Small And Medium-sized Enterprises
- Summary Of Best Practices In Cabinet Layout And Cable Management From German Computer Room Technology
- How To Query The Hong Kong Server Port And Perform Port Mapping And Forwarding
- Popular tags
-
Revealing The Behind-the-scenes Stories And Production Of Korean Movies
this article reveals the behind-the-scenes stories and production of korean movies, and explores the important roles of directors, screenwriters and producers in the korean film industry. -
How To Use Korean Native Family Ip Proxy To Prevent Being Blocked And Abnormal Login
this article introduces high-level protection methods on how to reduce the risk of being blocked and abnormal logins under the premise of compliance when using korean native home ip proxy, including risk identification, compliance principles, equipment consistency and monitoring suggestions. -
Detailed Explanation Of The Steps And Precautions For Opening A Native Korean Ip
detailed introduction to the steps and precautions for opening a korean native ip to help users better understand and operate.