All articles containing the tag [
Encryption
]-
How Do Developers Integrate Vietnamese Native Proxy IPs To Implement A Stable Multi-threaded Collection System?
Practical Guide for Developers: How to integrate native Vietnamese proxy IPs to build a stable multi-threaded data collection system. Covers IP types, authentication methods, connection pooling, rotation strategies, health checks, and anti-detection essentials.
Vietnamese Native Proxy IP Multi-threaded Collection Proxy Integration Proxy Pool IP Rotation Anti-crawling Strategy Stability -
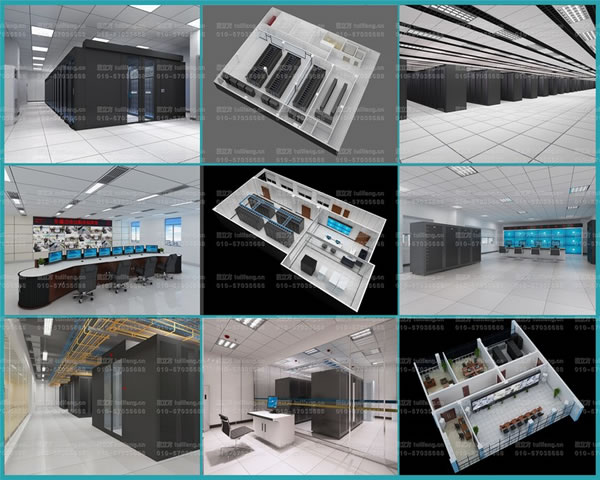
Ktv Operators Refer To Thailand’s Ktv Server Selection And Live Song Request System Layout
a reference guide for thai ktv operators, analyzing the key points of ktv server selection and live broadcast song request system layout, including practical suggestions on performance, storage, network, functional modules and security backup.
Thailand Ktv Server Ktv Server Selection Live Broadcast Karaoke System Ktv System Layout Ktv Operation Live Karaoke -
How To Practice Hybrid Deployment Of Enterprise-level Applications Between Hong Kong Cn2 And Lightweight Cloud
practical guide for enterprises: analyzes how enterprise-level applications are deployed hybridly between hong kong cn2 and lightweight cloud, covering key points such as network topology, routing strategies, security compliance, monitoring and continuous delivery.
Hong Kong Cn2 Lightweight Cloud Hybrid Deployment Enterprise-level Applications Cross-border Network Deployment Practice Network Optimization Cloud Architecture -
Does Alibaba Cloud Have Servers In Vietnam? Deployment Strategies And Suggestions In Cross-border E-commerce Scenarios
this article discusses alibaba cloud's availability in vietnam and its deployment strategy in cross-border e-commerce scenarios, including regional selection, cdn acceleration, network interconnection, data compliance, and multi-active disaster recovery recommendations to help companies optimize vietnamese user experience.
Alibaba Cloud Vietnam Server Cross-border E-commerce Deployment Strategy Cdn Acceleration Data Compliance Cross-border Dedicated Line Multi-active Disaster Recovery -
In-depth Comparison Of Hong Kong Mainland Server Ip Address And Domestic Proxy Speed Performance
this article provides an in-depth comparison of the performance of hong kong server ip addresses and domestic proxies in terms of speed, latency, packet loss, and stability. it provides test methods and actual scenario selection suggestions to help make decisions about network deployment and optimization.
Hong Kong Server Mainland Server Ip Address Domestic Proxy Speed Performance Delay Bandwidth Packet Loss Network Optimization -
Vps Lines Bypass Hong Kong And Use Kt Isp Strategy Analysis And Anti-circuit Optimization Plan
analyze the causes and detection methods of vps lines bypassing kt isp in hong kong, and provide anti-circuit optimization solutions such as bgp, transmission tunnels, dns and monitoring, which are suitable for geo and network operation optimization.
Vps Detour Hong Kong Ktisp Policy Anti-detour Optimization Bgp Routing Traffic Engineering Monitoring Traceroute -
Mirroring And Backup Management Practice Teaches You How To Ensure Data Protection For Alibaba Cloud Thailand Cloud Server
practical guide: help alibaba cloud thailand cloud server implement verifiable and recoverable data protection measures through methods such as mirroring, snapshots, automation, and off-site backup.
Alibaba Cloud Thailand Cloud Server Mirroring Backup Management Data Assurance Snapshots Off-site Backup Disaster Recovery Backup Strategy -
Best Practices For Deploying Hong Kong Cn2 Dedicated Line Servers To Improve Game And Software Distribution Experience
introduces the best practices for deploying hong kong cn2 dedicated servers to improve game and software distribution experience, covering network architecture, caching strategies, traffic management, security and operation and maintenance recommendations, suitable for seo and regional optimization.
Hong Kong Cn2 Dedicated Line Server Game Acceleration Software Distribution Delay Optimization Bandwidth Management Cdn Deployment Operation And Maintenance -
Implementation Of Cloud-network Interconnection Solution In The Context That Huawei Cloud Does Not Have Us Servers
discuss the implementation of cloud-network interconnection solutions under the background that huawei cloud does not have us servers, covering practical suggestions such as architectural strategies, cross-regional multi-cloud interconnection, dedicated lines and sd-wan, performance optimization, security and compliance, etc.
Cloud Network Interconnection Huawei Cloud Us Servers Cross-regional Interconnection Multi-cloud Dedicated Line Sd-wan Latency Optimization Compliance Data Sovereignty