All articles containing the tag [
Risk Assessment
]-
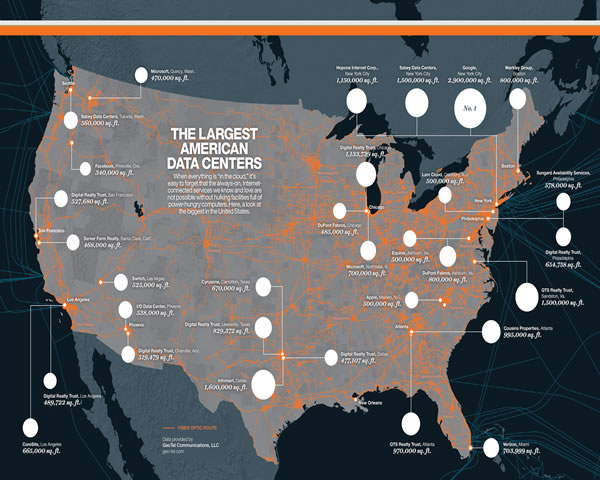
Cost Control And Optimization Recommendations For Long-term Maintenance Of High-security Servers In The United States
This article provides professional recommendations regarding the cost structure and optimization approaches for long-term maintenance of high-security servers in the United States. It covers areas such as resource allocation, bandwidth and network optimization, security policies, monitoring automation, and compliance considerations, helping enterprises to ensure security while maintaining controllable costs.
High-security servers in the United States: cost control optimization recommendations operations and maintenance of high-security servers bandwidth optimization security policies monitoring automation -
Cost Control And Optimization Recommendations For Long-term Maintenance Of High-security Servers In The United States
This article provides professional recommendations regarding the cost structure and optimization approaches for long-term maintenance of high-security servers in the United States. It covers areas such as resource allocation, bandwidth and network optimization, security policies, monitoring automation, and compliance considerations, helping enterprises to ensure security while maintaining controllable costs.
High-security servers in the United States: cost control optimization recommendations operations and maintenance of high-security servers bandwidth optimization security policies monitoring automation -
Disaster Recovery Switching And Recovery Strategies For Deutsche Telekom Computer Room Lines In Disaster Recovery Scenarios
this article discusses the disaster recovery switching and recovery strategies of deutsche telekom computer room lines in disaster recovery scenarios, including risk assessment, physical and logical redundancy, automated switching, monitoring and drills, and recovery verification, and provides implementable best practice suggestions.
deutsche telekom computer room disaster recovery switching disaster recovery line redundancy disaster recovery strategy bgp switching fiber optic multi-routing monitoring and drills -
Monitoring Settings And Capacity Planning Suggestions To Prevent Vietnam Game Server Failure In Advance
systematically introduces monitoring settings and capacity planning suggestions to prevent vietnam game server failure in advance, covering key indicators, threshold settings, capacity assessment and automated response strategies to help improve stability and user experience.
vietnam game server monitoring capacity planning fault prevention alarm elastic expansion network delay cpu memory -
Research On Safety Regulations For The Routing Of Traces In German Telecommunication Facilities And Solutions For Cross-regional Connectivity
This article examines the safety regulations regarding the routing of cables in German telecommunications data centers, as well as strategies for cross-regional connectivity. It covers legal requirements, physical cabling practices, EMC and fire protection considerations, redundancy design, and practical recommendations for fiber optic transmission.
Deutsche Telekom data centers route planning safety standards cross-regional connectivity fiber optic cabling redundancy design network reliability data center specifications -
Network Solution For Small And Medium-sized Enterprises: Backup And Redundancy Design To Avoid Telecommunications Failure To Connect To Us Servers
network solutions for small and medium-sized enterprises, introducing how to avoid the risk of telecommunications being unable to connect to us servers through backup and redundancy design, including link redundancy, sd-wan, bgp, dns/cdn, monitoring and security strategies.
small and medium-sized enterprises network solutions telecom unavailability us servers backup redundant design sd-wan bgp dns cdn failover monitoring -
Supply Chain Challenges Of The U.s. Server Hosting Industry In The Context Of Sino-u.s. Trade
in the context of sino-us trade friction, this paper analyzes the supply chain challenges of the us server hosting industry in terms of hardware procurement, software compliance, logistics and data sovereignty, and provides suggestions for solutions.
sino-us trade us server hosting supply chain challenges data sovereignty hardware procurement cybersecurity logistics risks -
Deployment Considerations Under Singapore And Hong Kong Cn2 Compliance And Data Sovereignty Requirements
in view of the compliance and data sovereignty requirements of singapore and hong kong under cn2 network conditions, it provides deployment considerations, architectural suggestions, logging and auditing practices, as well as contract and supply chain management points from a technical and compliance perspective.
singapore hong kong cn2 compliance data sovereignty deployment considerations cross-border data data protection network deployment -
Countermeasures Against The Risk Of Sudden Cable Breakage And Disaster Recovery Practice Of Cn2 Submarine Optical Cable In Taiwan
this article introduces strategies to deal with the risk of sudden cable breakage, focusing on the characteristics of cn2 submarine optical cables and taiwan's disaster recovery practices, covering prevention, monitoring, redundancy design and emergency response suggestions, and is suitable for network operations and data center planning.
broken cable cn2 submarine optical cable taiwan disaster recovery disaster recovery network redundancy submarine cable monitoring